Our Expertise,
|
We are pioneers in deployment, integration and customization of these technologies, involving track record for Microsoft Case Studies from our engineers since 2007 First Ever MS Service Manager - Provance Asset Management Pack from Provance implementation of the region with great ROI to the organization Case Study First Ever Exchange deployment in Whole GULF for 2007 version, in Qalhat LNG* Case Study First Ever Private Cloud Deployment at Pakistan Petroleum Limited Case Study Biggest Microsoft Service Manager deployment in Pakistan at Habib Bank Limited Blog Post First Ever IEEE 802.1x implementation, only premises in Pakistan with all wired and wireless switches protected through Microsoft Network Access ProtectionBlog Post First Ever Microsoft Identity Manager Implementation in Oman at Central Bank of Oman, Complete Identity synchronization between active directory, HR System, Oracle ERP and all other repositories* Blog Post |

|
Our Quality,
|
Following only Consultancy as our work, we follow Microsoft Microsoft Operations Framework and Microsoft Solution Framework 4.0 as our solution deployment and operation frameworks so that quality execution is delivered technically. Instead of being reliant on just the onsite consultant from our end, We use combination of onsite and offsite consultants with powerful collaboration tools like Microsft Lync, SharePoint to ensure that quality implementation and work is performed regardless of the experience of onsite only consultant from our end.
We are practicing the same for five years by now, giving us versatility, reliability and resourcefulness in handling the same technologies group. Being the Silver compentency partner for Microsoft we are fully backed by Microsoft in terms of advisory hours and support incidents back to back with Microsoft, while we are executing our work. |
|
We recommend,
-
ENABLE
Enable ITIL based incident management, change management and problem management alongwith request fulfillment using Microsoft Service Manager 2012 R2. We at MetalSoft hold the largest deployment base of this technology in the region, starting with organizations like Habib Bank Limited. Complete SLA based tracking and ITIL standard help desk implementation is achieved through Microsoft Service Manager 2012.
Enable ITIL based Asset Management using Provance Management Pack for Service Manager 2012. Provance is the recommended solution for Asset Management by Microsoft and it uses the same CMDB developed and populated by Microsoft Service Manager and powered by other system center products. MetalSoft did the complete end to end deployment of this solution at Pakistan Petroleum Limited with marvelous outcomes. Check out our recent case study Case Study. 
Enable ITIL based Event management using System Center Operations Manager as well as we can provide you visio based designing of dashboards and score cards for monitoring. Properly deployed System Center Operations Manager ACS can allow easy forensic analysis on any security breach of the organization.
-
SECURE!
Are you worried about document security and information leakage?. Let us help you with Microsoft AD-RMS 128 bit encryption along with Federation outside to other organizations as well as MSN identities. It can be made to work even on blackberry and Apples devices. 

Centralize you authentication using Active Directory as source of identity for all applications using IdMfamily of products from Microsoft. Replication based solution from Microsoft allows to sync all identity stores from Oracle, IBM, Lotus, HR Modules and other platforms and applications with Active Directory. This allows automatic provisioning and deprovisioning of users accross multiple applications in organization and makes overall identity management automatically managed. Centralize your authorization using AzMan component of Microsoft for Active Directory. It is natural and easy to provide rights and permissions across the enterprise various applications like Oracle, IBM, SAP using Active Directory groups and users and AD-Snap Ins like of AzMan. Microsoft provides Authorization Management Solution built right into windows server Operating System to help achive that. 
Implement enterprise Single Sign On (SSO) between various applications like SAP, Oracle, IBM and windows active directory. Using Microsoft Active Directory Federation Services, it is possible to program this functionality. If your antivirus is being updated but not your windows desktop Operating systems, then you are only half way to be secured. With MS System Center End Point protection deployed on top of MS SCCM, patching for both is performed and handled under same framework. 

Either you develop floor wise VLANs on network switches or rooms wise. With Microsoft Network Access Protection it is possible to design your network to segment based on membership of AD groups or attributes like departements which is more logical break down. 802.1x capable switches allows that. MetalSoft is first organization to enable such functionality in Pakistan, check our corporate profile below. Also with NAP you can block access to your network switches (wired as well as wireless) so that AD-domain joined machines land into a different network VLAN from guests besides auto remediation of missing OS patches. 
You are worried about centralization of audit logs of all the critical servers and services but servers often run of limited log space. Consider MS System Center Audit Collection Services so that temper resistant, consolidation audit database can be developed with no worry for lossing crucial audit data. -
FEDERATE
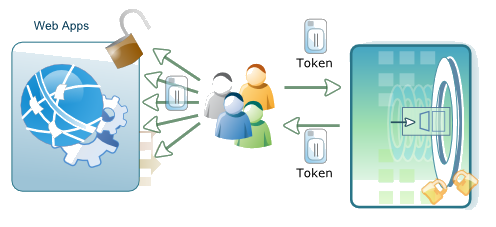
Properly deployed Active Directory Federation Services allow the seamless single sign-on experience, despite the location of service rendered from(cloud or onpremises) or nature of technology (from same principal or not). The latest XAML token based technologies can exchange authentication tokens to provide seamless experience to end users who don't need to bother with login again and again.
Microsoft Direct Access allows that end user VPN is established while the operating sytem is booting up, so that even the group policies are applied to the machine, as provided from remote servers. This is particularly required for perfect control on mobile uesrs with laptops and tablets.
Check our profile for information on our customers and deployment examples and follow up with us for detailed information on any of the above.
